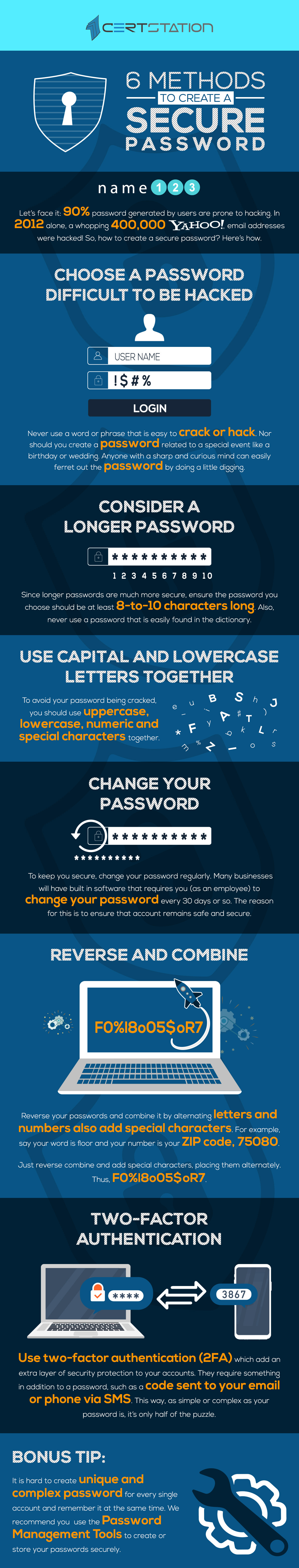
You are required to have a safe and secure password for nearly every account you make online. Choosing one that others, especially hackers, find difficult to comprehend needs the creation of random letters and word combinations. Fortunately, creating passwords that are hard to crack and easy to remember is not as difficult as it sounds provided a few points are kept in mind.
A strong password is generally longer than usual, consisting of a combination of letters (upper and lower case), numbers and symbols. Also, a strong password does not need to contain any personal information, and a word that doesn’t exist in a dictionary also makes for a password that is hard to crack.
How are Passwords Hacked?
When cyberthieves conduct massive hacks, as they have lately done with popular email servers, the lists of affected email addresses and passwords are generally leaked online. And they do it with a high degree of ingenuity. Here are the four methods hackers adopt to hack passwords.
1. Brute Force Attack
An attacker tries various combinations of a targeted password with the hope of eventually guessing correctly. The longer the password, the more combinations that will need to be tested.
2. Dictionary Attack
A dictionary attack seeks to beat a verification mechanism by methodically entering each word in a dictionary as a password or trying to find out the decryption key of an encoded message or document. Hackers often succeed in launching this attack as many individuals and companies use ordinary words as passwords, which are easily found in a dictionary.
3. Phishing
A phishing email leads the unwary reader to a fake login page linked with any service the hacker wants to access, requesting the user to fix some awful problem with their security. That page then scans their password and the hacker can use it for their own purpose.
4. Rainbow table attack
Rainbow tables allow you to bring a rainbow table into a list of pre-computed hashes, containing all conceivable password combinations for any given hashing algorithm. Rainbow tables are striking as it decreases the time needed to crack a password hash to just looking something up in a list.