Software giant Microsoft has said that an Emotet infection managed to take down an organization’s whole network by overheating all computers
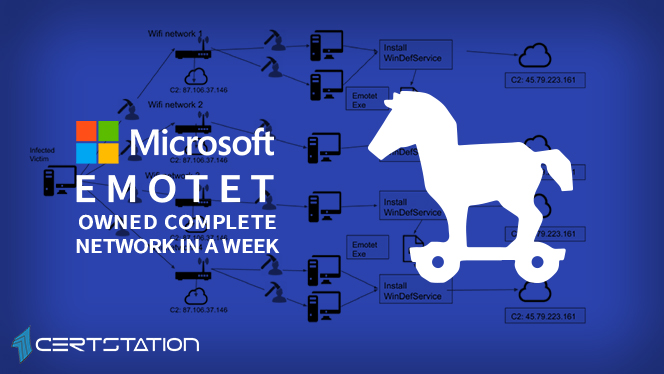
“After a phishing email delivered Emotet, a polymorphic virus that propagates via network shares and legacy protocols, the virus shut down the organization’s core services,” DART said.
“The virus avoided detection by antivirus solutions through regular updates from an attacker-controlled command-and-control (C2) infrastructure, and spread through the company’s systems, causing network outages and shutting down essential services for nearly a week.”
The Emotet payload was delivered and executed on the systems of Fabrikam — a false name the software behemoth gave the victim in their case study — five days after the employee’s user credentials were exfiltrated to the attacker’s command and control (C&C) server.
The surveillance camera network of the company along with the finance department were also affected by the incident.
Related Article: Emotet Malware: A Threat Distributor
“Emotet consumed the network’s bandwidth until using it for anything became practically impossible. Even emails couldn’t wriggle through.” continues the report.
Microsoft specialists effectively controlled the Emotet infection and removed the malware from the infected network, then it deployed Microsoft Defender ATP and Azure ATP trials to spot and eliminate the malicious code.
The Emotet banking trojan has been active at least since 2014, while the botnet is run by a threat actor traced as TA542.
In 2019, security specialists haven’t noticed any activity related to Emotet since early April, when experts at Trend Micro have exposed a malware drive distributing a new Emotet Trojan variant that affected devices and uses them as Proxy C2 servers.
Emotet resurfaced on the threat landscape in August 2019, with an active spam distribution movement. At the time, Malwarebytes noticed the Trojan started giving spam, spam messages originally targeted users in Germany, Poland and Italy, and also the US.
The drive continues to attack users in Austria, Switzerland, Spain, the United Kingdom, and the United States.




