Web-based Ethereum wallet, Shitcoin Wallet, is pushing malicious javascript codes to the wallet users, thieving critical information.
Exposed by Harry Denley, a security and anti-phishing expert, on Monday, the susceptible codes are gathering IDs of main crypto platforms including Binance, MyCryptoWallet, and many others.
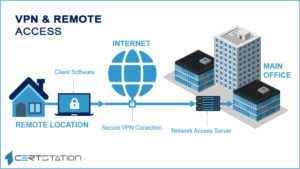
The Wallet works as a Chrome extension that downloads tons of javascript files from a distant server. The code then looks for any open tabs on the web browser covering pages of any digital asset connections and Ethereum network tools to fix the data in those windows.
The malicious codes send all the data to a remote server recognized as “erc20wallet.tk.” The top-level domain belongs to a group of the south pacific island terrain of New Zealand called Tokelau.
Intended to hold Ethereum and other ERC-20 tokens, the company claims that it has over 2,000 users. The platform essentially works as browser extensions, although the company says there is a desktop application for Windows.
“It is a web wallet which has several extensions for different browsers,” a blog post by the company explained.
In the meantime, many browser extensions were found in the past with malicious codes. Nevertheless, most of those were involved in the unlawful removal of digital currencies on victims’ computers.
Most lately, Google barred extensively used Ethereum wallet and DApp browser MetaMask for violating its monetary policy from Play Store. Though not quantified, the technology behemoth was signifying the crypto mining feature, which is severely bans in its policy. Remarkably, the platform does not offer any crypto mining services to its users.